Building stakeholder relationships with Service Desk and End User Computing
This article is the second of a four part series by AJ Witt of ITAM Review written in collaboration with ServiceNow’s Ryan Wood-Taylor & Peter Beruk. The series outlines how a strategic ITAM practice will deliver enhanced business value through creation of strategic stakeholder relationships.
- Part One – How strategic ITAM can build business value, and how you can take your team on that journey
- Part Two (this article) – Building stakeholder relationships with Service Desk and End User Computing
to be followed by;
- Part Three – Engaging your Security Operations team in your ITAM programme
- Part Four – Working with Architects & Business Analysts to specify new products and services
The full article series is also available as a whitepaper, downloadable here (no registration required)
Your End User Computing (EUC) & Service Desk teams are vital stakeholders for effective ITAM, working in the Deploy, Service/Operate, and Retire lifecycle phases. They’re the people who get hardware and software in the hands of your users and are the public face of IT.
Having worked in such a team I can attest that is a high-cadence, stressful place to be. Demands are constant, scale is large, and work is often unpredictable. As a function they are very much focused on the here and now. They manage everything from legacy apps to requests from users running shadow IT, hardware issues and provide service to everyone from the front desk to the C-Suite.
This article examines what these teams do, dives deeper into a key process – Build, and suggests approaches to improve engagement. These approaches lay the foundations for the day-to-day delivery of ITAM goals through alignment with business-as-usual activities.
What they do
EUC & Helpdesk teams receive service requests from users for hardware and software. They process incidents relating to the entire IT infrastructure – everything from a forgotten password to a major service outage. They may be an in-house resource or be provided by a third party or managed service. They work very closely with users and are very much the public face of IT. They build strong relationships with the departments and users they serve, sometimes to the detriment of IT and the organization. Throughout my career I’ve seen support engineers be socially-engineered by departments and individuals keen to get the latest kit, or bypass process to get software installed. Being young and ambitious they’re often over-helpful, particularly for demanding users.
To counter this unequal relationship, I’ve seen a variety of approaches by EUC & Helpdesk Team Managers. For EUC there may be a “Build Room” with controlled access, meaning users can’t drive-by the engineers and put requests in. Helpdesk agents may only be contactable via a shared contact number. Most will have policies stating that all requests need a ticket logged with Helpdesk before any action will be taken. There will be VIP support teams set up to serve the most demanding users such the C-Suite. Many also run dedicated teams for business-critical in-house functions such as Customer Contact Centres.
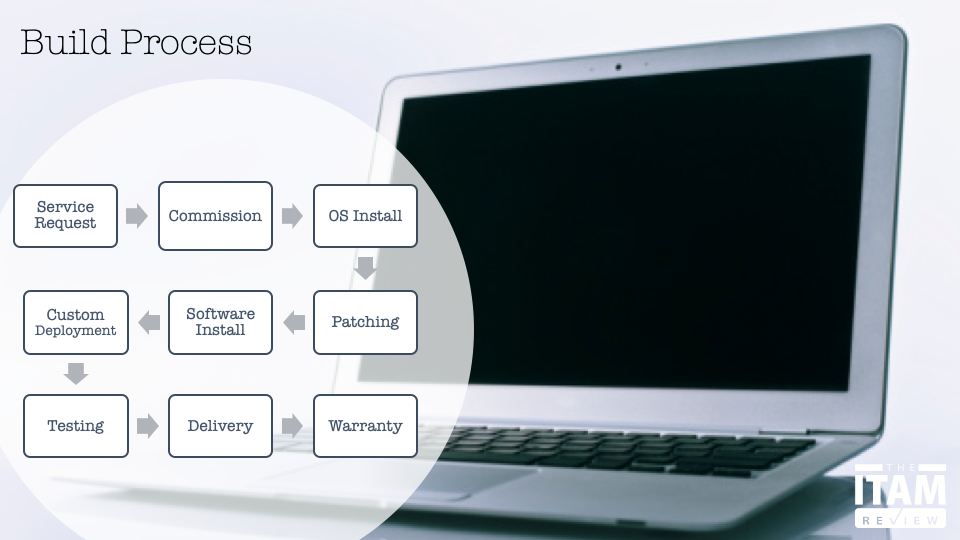
To dig a little deeper into what these teams do let’s look at the Build process for deploying a new laptop.
The Build Process
So, what’s involved in building a laptop? Build is split into the following phases:
- Service Request – the process for requesting and authorising acquisition of the laptop.
- Hardware commissioning – getting the laptop out of the box, powered on, and checked.
- OS install and activation – most organisations will deploy a custom Operating System image on their laptops, often referred to as a “gold master”. At this point the domain computer account will be created and the laptop added to the domain. Automation has a role to play here, and in some cases larger organisations will receive kit pre-configured laptops with their master build installed
- Patching and updates – the pace of change is such that all laptops will need patching with security fixes and other updates.
- Software Installation – standard software packages will be installed and activated.
- Custom deployment – any “special-request” software not usually deployed widely in the estate – for example engineering software
- Test – typically the laptop will be left powered-on and connected to the network for a period of time to ensure there are no hardware or software issues.
- Delivery – the laptop is delivered to the user either by hand or by delivery
- Warranty Support – many EUC teams run a warranty period for newly-issued hardware whereby the user can receive priority support
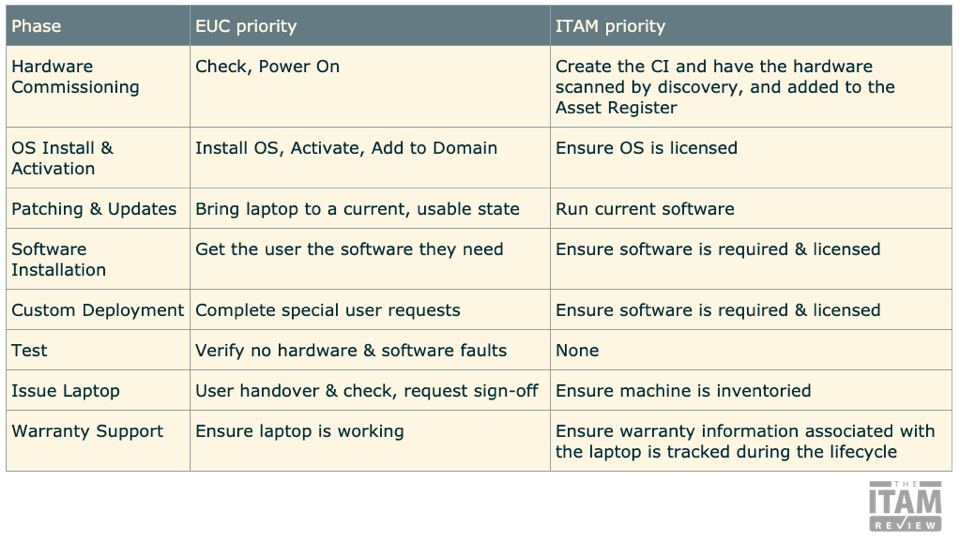
ITAM vs EUC Priorities
Based on the above build process the priorities of each team can be summarised as follows:
The Challenge
The Build process is time-consuming with a lot of moving parts and to-and-fro between EUC & the user. Often, EUC will have received the request late, and the user will need it to be completed yesterday. Anything that gets in the way of delivering that laptop will be short-cutted, incomplete, or just plain ignored. Whilst automation has an increasingly large role to play here, there is still manual intervention required and therefore risk of human error.
EUC teams operating in this way will inevitably build up license non-compliance positions. If they’re measured on number of requests closed, licensing won’t be checked. You need to ensure your engineers to meet ITAM objectives too – summarised as only installing authorised, licensed, required, and serviceable software.
Stakes in the game
So, how do you address this challenge? First, you need to add value for your frontline teams. Second, you need to find a way to align your goals and deliverables with theirs. If that isn’t possible then policy changes and reporting/KPIs may be required to enforce compliance.
To recap, the key motivators for EUC Teams are;
- Getting the incident or request closed
- Getting the laptop built and issued quickly
Analysing this further, the needs of each stakeholder can be summarised as follows
- Users are happy when they get the laptop they want, with the software they need to do their job, delivered on-time
- EUC Teams are happy when a build is done quickly and efficiently using the right software
- IT Managers are happy when the above is done according to process and within budget
- ITAM Managers are happy when the asset is being inventoried correctly for HAM/SAM purposes and all software installed is in-use and no license compliance issue has been generated
- CIOs are happy when they receive positive reports regarding IT service levels and costs aligned to budget expectations
Bringing this all together we can see that there is an overlap in motivators and goals that can be further summarised as follows:
Cost & risk is minimised when laptops are built quickly and the correct software is installed, licensed, and used.
And;
Users are happy when laptops are built and delivered quickly with the software they need to do their job.
ITAM Processes & Procedures for EUC
The following are some processes and procedures that will align ITAM, EUC, and ServiceDesk to deliver great service for your users.
Provide the front-line teams with Inventory data
Accurate and available inventory information allows front-line IT teams to close requests & resolve incidents more quickly. It enables them to immediately identify which machines are in use by which users and when, and potentially use IP address or other location data to track down the physical location of assets. Inventory data provides them with critical software deployment data such as OS version and patch level, and which applications are installed on a given machine.
Just the above information can cut hours from a Service Request. It also heads off version-creep when laptops are rebuilt or replaced. Version creep is where an end user states that they had some expensive version of software on their old laptop and absolutely must have it on their new one – Pro versions of Office applications, or full versions of Autodesk products, or non-reader versions of Acrobat are common requests. If the front-line teams can see that they weren’t installed on the old laptop, they can push back on the request and cut down on wastage. They can’t do that without your inventory data to back them up.
Make license compliance the responsibility of EUC & Service Desk
This will be a controversial request, but a necessary one. Work with your senior management to develop policy statements that make the front-line teams responsible for ensuring that only software for which you own licenses is installed. Put appropriate policies in place regarding Shadow IT. Individual agents and engineers must be responsible for this otherwise license compliance checks may be skipped when SLA deadlines loom. Remember license non-compliance is often generated when the application is first installed, not first used, and this policy protects your organisation from that. Similarly, for SaaS, you’re ensuring that sensitive data is protected by only using services that have been vetted by your compliance teams. You’re closing the stable door before the horse has bolted.
Provide accurate and timely license availability data
In order to make license compliance the responsibility of front-line teams you have to ensure that timely & accurate license availability data is available. Manually reviewing IT Requests for software license compliance is a tedious and time-consuming activity and often error prone. If ITAM becomes a bottleneck, it will be bypassed or blamed for getting in the way of delivering excellent customer service and achieving organizational objectives such as providing the right tools for employees to do their jobs.
It is your choice whether you give front-line teams access to entitlement data information in your SAM tool. I’d recommend you only do this if you have utmost confidence in your data and permissions are fine-grained enough to limit access to just the data required to check license availability. An alternative approach I used was to produce a weekly summary report for commonly-installed applications and then just handle the special requests manually. Finally, if your tool and processes support it, it may be possible to automate license compliance checks.
Incentivise front-line teams to optimise software deployments
Laptop rebuilds and upgrades are common tasks for EUC Teams, and often more time-consuming than issuing a brand new device. User settings and data need to copied across for example, along with any application customisations. To ensure software deployments are optimised it is important to ensure at this stage that only previously-used software is re-installed. Not only does this prevent license wastage it also cuts the build time for the EUC team.
To enable this, provide your EUC teams with access to usage data. The engineers are then able to quickly determine whether an application is in use. This is a great way of getting back those unused Adobe, AutoCAD, Visio, and Project licenses – all software applications notorious for being under-utilised.
Furthermore, incentivise your front-line colleagues by reporting on the value of unused software that they recover. Those colleagues rarely get the opportunity to demonstrate they’re saving the organisation money and even a few thousand dollars of recovered software per month is worth celebrating. In a previous role adopting this approach enabled an engineer to save around $7k by reclaiming unused Visio licenses during a rebuild project – resulting in a monthly service award for that engineer. This is a great way of building rapport and demonstrating that ITAM can drive service delivery and cost-savings side-by-side.
Keep accurate records to streamline deployment of non-standard software
Much of your software may be covered by volume license agreements with shared license/activation keys, or no keys at all. However, for non-standard applications that are licensed individually, it is vital you keep a record of serial numbers, product keys, named users, and install media. You also need to ensure that in the event of a rebuilt or replacement laptop that the license key has been freed up properly from the old machine. You need to provide the serial numbers and other information to the EUC team in an easily-accessible but secure form. Once again, there are opportunities for automation here.
Failure to keep accurate records slows down the build process and frustrates end users who need specialist software to do their job. You don’t want to lock your Senior Designer out of AutoCAD for a minute longer than is necessary. The people in the firing line are your front-line teams – you owe it to them to provide accurate data in a timely fashion to serve their customers as efficiently as possible.
Building an automated service delivery framework
Much of this article has focused on practical aspects of day-to-day interactions between people in Service Desk, EUC, and ITAM teams. These human interactions are vital when you’re working to optimise the fulfilment service being provided to your customers. You will deliver service improvements by following them, but ultimately you will hit a barrier caused by the sheer scale and cadence of the tasks at hand. This is where automation plays a role, and where having a close stakeholder relationship with your front-line teams will really accelerate your ability to deliver world-class ITAM.
So, what does automation look like? Well, it began with software deployment tooling enabling the packaging and management of common applications – tools such as SCCM have been in place to deliver this for many years. Where next-generation automation comes to the fore is in building compliance checks and service enhancements around those tools. One such approach is Enterprise App Stores.
Enterprise App Stores
Enterprise App Stores provide end-users with the ability to request their own software without any involvement from Service Desk or EUC. Requests can be pushed into a workflow whereby their line manager authorises the request and a check is made to ensure licenses are available – thereby ensuring license compliance.
App Stores and automation also facilitate the removal of software. Rules can be created to automatically remove unused software based on usage data gathered by your SAM tool, with jobs being automatically created in your deployment tool. And because users are able to request apps via self-service there shouldn’t be significant disruption in the event that they subsequently require that application.
Delivering such an automation project is complex and depending on the buy-in your ITAM team has, may be challenging to deliver alone. By enlisting the support of your front-line teams, you can begin to build critical mass behind the project and make it about customer service rather than compliance. Service is often a more compelling motivation for senior leaders, particularly with an increasing focus on improving employee experience.
Summary
It is hopefully clear that front-line teams, users, and ITAM teams share a number of common goals. By identifying these shared goals – such as timely delivery of the right laptop with the right licensed software – you can work with those teams to develop processes and tools to improve user satisfaction. And you can do that whilst ensuring license compliance is not impacted and even potentially reduce software usage across your estate. Everyone in this case does win.
Further Reading
For more on how modern, integrated ITAM tools reduce risk, increase visibility, improve service, and optimise software spend see this whitepaper – https://www.servicenow.com/lpwhp/next-generation-software-asset-management.html
Related articles:
- Tags: Build Process · Engaging stakeholders · EUC · HAM · Laptop Build · service desk · ServiceDesk · ServiceNow · Stakeholder Engagement · stakeholder management