Oracle launches middleware verification for SAM tools

Benjamin Vidal, Icon Consulting.
This article has been contributed by Benjamin Vidal, Icon Consulting.
Following the SAM tools verification for Database and Options, Oracle has launched a similar campaign for its Fusion Middleware products. This article looks at the following questions:
-
- What does this Oracle verification mean?
- Which SAM tools are verified by Oracle and for which products?
- Which products will be covered by this new verification?
- What can be inferred about Oracle’s audit plans?
The “Verified Third-Party Tool Vendors”
On its web page, Oracle LMS has published a list of verified SAM Tools.
https://www.oracle.com/corporate/license-management-services/tooling.html

Perhaps surprisingly, Snow is not on that list.
Editor’s note: Christian den Boer, Director of Enterprise Applications at Snow Software said “Snow’s goal is to gain Oracle verification… We look forward to expanding our engagement with Oracle and hope to join the vendors verified by Oracle LMS for their Fusion Middleware in the future.”
It is important to understand what this verification means:
Oracle only verifies the raw data collected by the listed SAM Tools. Under no circumstances will the SAM Tool’s interpretation of this data be enforceable against Oracle in the event of an audit.
More specifically, for this verification, Oracle provided the various SAM toolmakers with a set of standard queries (close to the Review_Lite.sql script and cpuquery.cmd/sh used by LMS during their reviews). All SAM Tools then have the requirement for verification to be able to produce an archive containing a csv document consolidating all outputs for each of the hosts and Database instances scanned by the SAM Tool:
- “Tools from the following vendors have been verified to provide data sets that supplement an Oracle LMS commitment.”
- Oracle LMS will accept data from any of these tools as an alternative to installing Oracle LMS measurement tools.
Currently, the verification only covers Database and Options products (Partitioning, Tuning Pack, etc.):
“The scope of the verification process only covers the data collection related to the installation and use of specific Oracle products, namely Oracle Database and associated options. The verification does not include any other Oracle products or the overall capabilities of the vendor’s solution”.
However, Oracle recently contacted the various SAM Tool publishers to communicate the specifications for the Fusion Middleware product set.
It is important to note that each SAM tool is free to define its own logic for interpreting database and options activations. In the event of an audit, LMS will make its own interpretation even if this interpretation is different from that of the SAM Tool.
As an example, some SAM Tools will consider a control_management_pack_access set to ‘DIAG + TUNING’ as sufficient usage evidence to require a license. For others, it requires the qualification of effective use of a feature associated with Diagnostic or Tunning Pack to be retained.
Similarly, not all SAM Tools have the same capabilities to analyze the storage and network isolation requested by LMS to its customers when calculating the processor metric with VMware environment.
- “Please note that the installation and use of a tool from a verified vendor does not replace an Oracle License Audit or revoke Oracle’s contractual right to perform one.”
- “In addition, the use data gathered from these tools will still need to be analyzed by the Oracle LMS organization to assess license needs and provide the customer with a compliance statement.”
Even in the event of verification, Oracle remains the sole judge of the application of its licensing rules. The choice of a Verified Third-Party Tool will not clear up any of the “grey zone” of Oracle licensing. However, it will provide a level of information equivalent to that of LMS for the management of your Database and Options assets.
What about Oracle middleware verification for SAM tools?
As previously stated, Oracle intends to extend this verification to the Fusion Middleware scope. The principle of this verification should remain the same.
Here again, LMS will specify to the publishers of SAM solutions its prerequisites in terms of raw data expected. However, the interpretation of these data will still remain up to the efforts engaged by the SAM Tools to study Fusion Middleware product’s activation causes.
Considering the principles applied for the Database and Options scope, LMS will seek to obtain the following three levels of information contained in its LMS_Collection_tools based on the keywords specific to the various Fusion Middleware products:
- Files: List of files related to Oracle Fusion Middleware software installations
- Processes: List of processes related to Oracle Fussion Middleware software execution to eliminate false positives resulting from the analysis of discovered files only.
- Configuration: Content of Fusion Middelware software configuration files (e.g., config.xml – domain-registry.xml for WebLogic). This level of detail is necessary for interpreting feature activations and therefore the editing level used for WebLogic.
Given the scope covered by the LMS_Collection_Tools it can be inferred that the products in Oracle LMS’ radar are now:
- Oracle WebLogic and Internet Application Server
- Oracle Service Oriented Architecture (SOA)
- Oracle Tuxedo
- Oracle Business Intelligence (now Oracle Analytics Server)
- Oracle WebCenter
- Oracle Forms and Reports
- Java SE
Beware, however, the level of information collected by these scripts allows you to have initial configuration information to spot Oracle application installations (E-Business Suite, Siebel, PeopleSoft). Indeed, WebLogic domain names and Java argument sets are opening doors to the Oracle Applications world and so it is perhaps reporting information that is out of scope.
It, therefore, seems likely to think that Oracle is targeting new perimeters that are still weakly controlled by its customers and carry significant compliance risks.
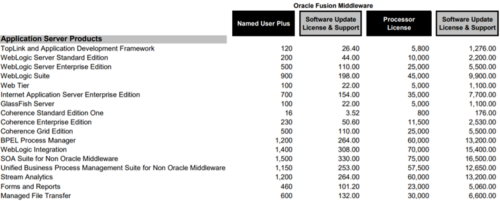
When looking at the “Application Server Products” section of the Oracle Technology price list, “Coherence server caches” can cost up to $25k / Processor if Grid Edition features (Federate Caching, Multitenancy, GoldenGate Hot Cache, etc.) are activated. This cache server is embedded in the standard WebLogic installer and only requires a few clicks for activation.
It is therefore important not to leave out of scope these middleware products during your internal SAM campaigns as they are often mis-detected and misinterpreted.
However, we must look on the bright side as well. This Oracle verification campaign will necessarily improve the SAM tools maturity with these Fusion Middleware software products – giving a better experience overall. It remains to be seen whether the publisher will also extend its scope to Oracle Applications products such as E-Business Suite, Siebel, PeopleSoft, Taleo, JD Edwards, etc. But it’s certainly a likely next step.
This article has been contributed by Benjamin Vidal, Icon Consulting.
About Guest Contributor
This post was written by a guest contributor. Please see their details in the post above. If you'd like to guest post for The ITAM Review please contact us.
